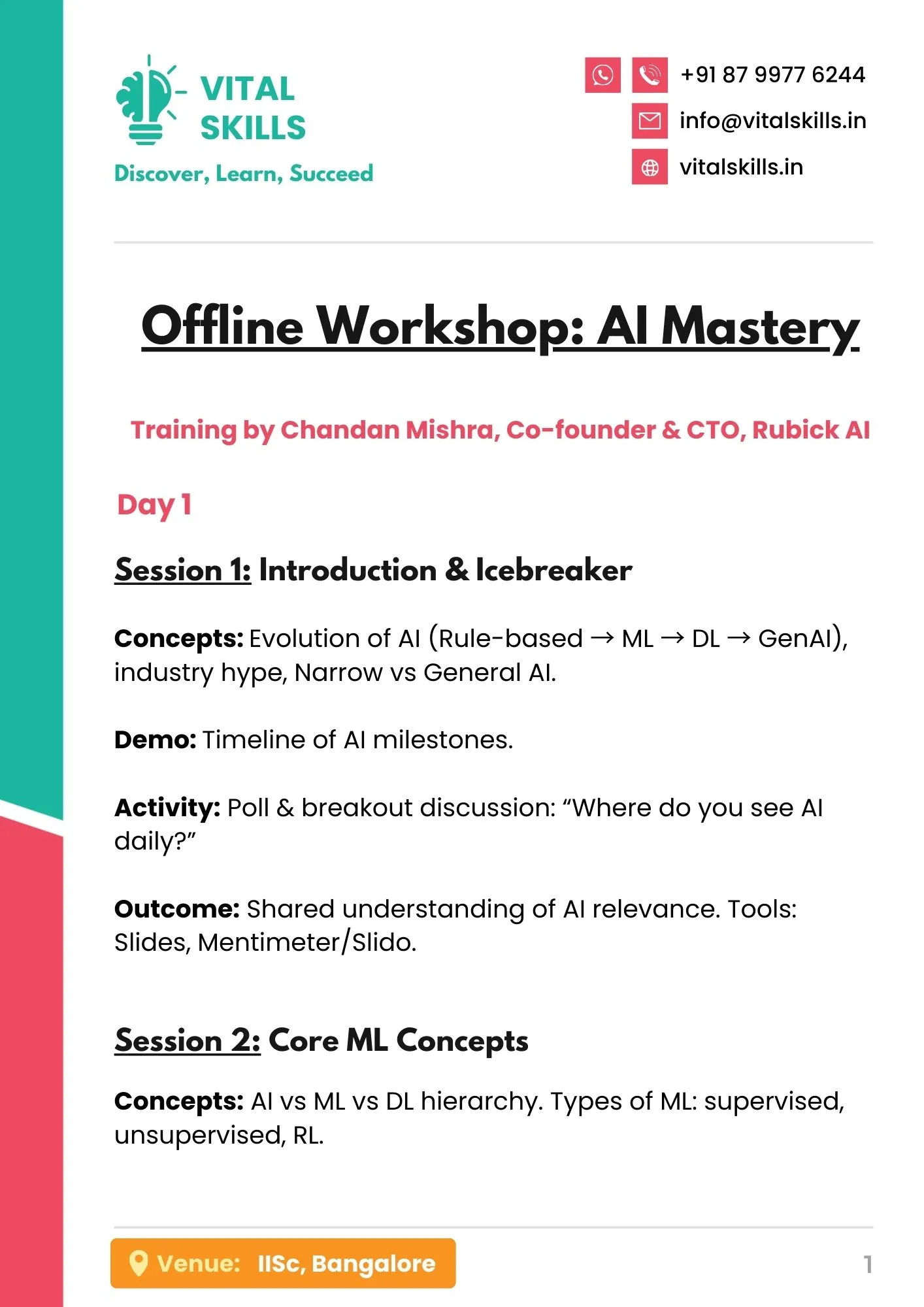
Ethical Hacking & Network Security
Unlock the secrets of cybersecurity with our Ethical Hacking Course. Dive into the world of digital defense as you learn to think like a hacker, uncover vulnerabilities, and fortify systems against cyber threats. Led by expert instructors, this comprehensive course equips you with the tools and techniques needed to safeguard networks, data, and critical infrastructure. Whether you’re a beginner or seasoned professional, embark on a journey to protect and secure with confidence.
₹4,999.00 Original price was: ₹4,999.00.₹599.00Current price is: ₹599.00.
About This Course
An Ethical Hacking and Security course equips students with the skills to identify, assess, and mitigate security vulnerabilities in computer systems and networks. The curriculum covers essential topics such as penetration testing, network security, cryptography, web application security, and incident response.
Additionally, students will explore cybersecurity frameworks, risk management, and compliance regulations, preparing them for roles that safeguard organizations against cyber threats. By the end of the course, graduates will be equipped to pursue careers as Ethical Hackers, Security Analysts, Penetration Testers, and Cybersecurity Consultants, playing a crucial role in protecting sensitive data and maintaining the integrity of information systems.
Course Content
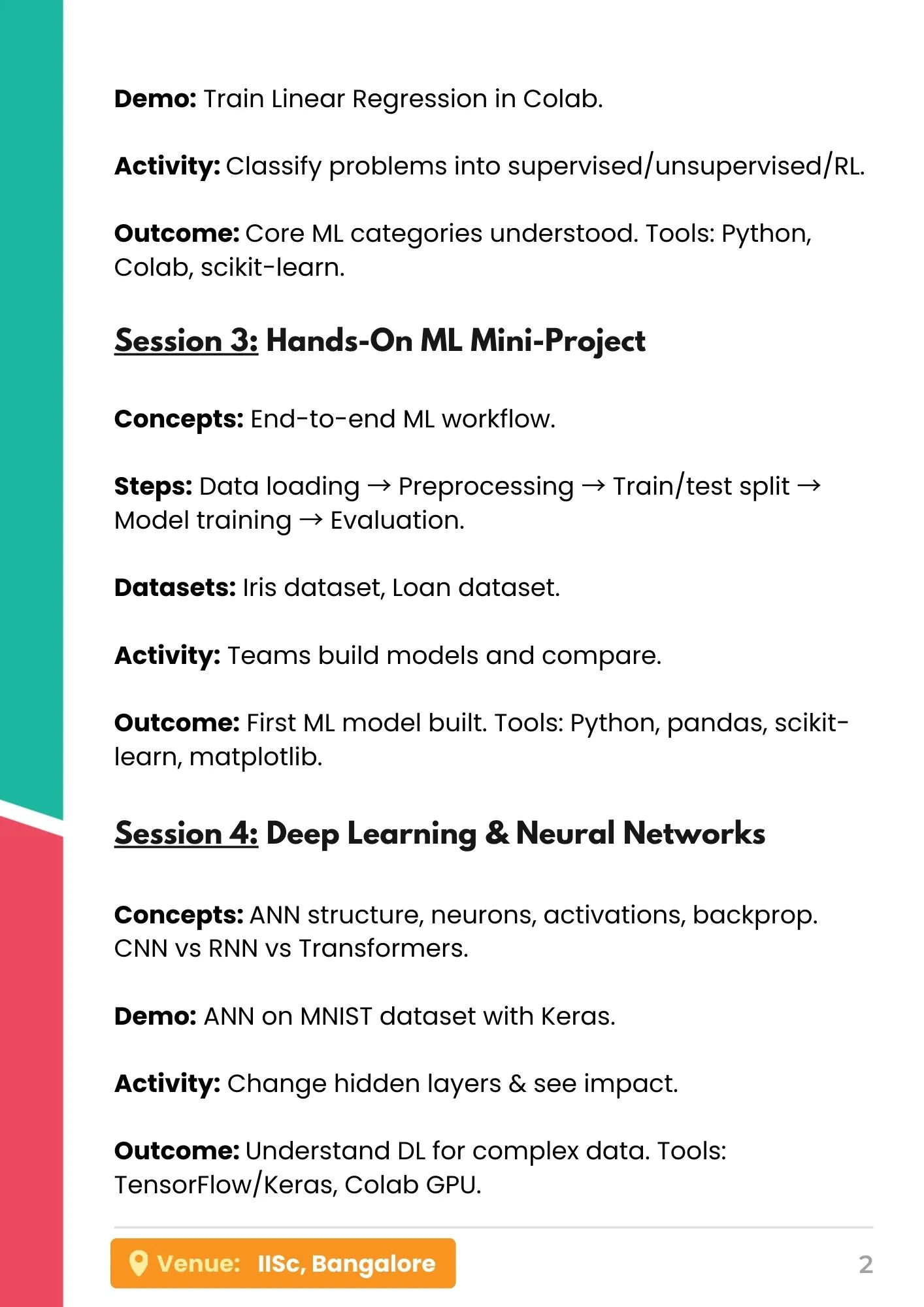
Module 1 - Introduction to Ethical Hacking
– Understanding Ethical Hacking and its Importance
– Differentiating Ethical Hacking from Malicious Hacking
– Legal and Ethical Considerations
– Overview of Common Cybersecurity Threats and Attack Vectors
– Introduction to Penetration Testing and Vulnerability Assessment
– Installing Linux, Linux Basics & File Permissions
Module 2 - Networking Fundamentals
– Basics of Computer Networks
– TCP/IP Fundamentals
– OSI Model and its Layers
– Understanding Network Protocols (e.g., HTTP, FTP, DNS)
– Network Scanning Techniques and Tools
Module 3 – Information Gathering and Footprinting
– Understanding Information Gathering Techniques
– Passive and Active Information Gathering
– Whois Lookup, DNS Enumeration, and Google Hacking
– Social Engineering Fundamentals
– Using Open Source Intelligence (OSINT) Tools
Module 4 - System Hacking
– Understanding System Architecture
– Exploiting System Vulnerabilities
– Password Cracking Techniques and Tools
– Privilege Escalation
– Malware Fundamentals and Countermeasures
Module 5 -Web Application Security
– Understanding Web Application Architecture
– Common Web Application Vulnerabilities (e.g., SQL Injection, Cross-Site Scripting)
– Web Application Scanning and Enumeration
– OWASP Top 10
– Web Application Penetration Testing Methodologies and Tools
Module 6 - Wireless Network Security
– Wireless Networking Fundamentals
– Wireless Security Protocols (e.g., WEP, WPA, WPA2)
– Wireless Hacking Techniques (e.g., Packet Sniffing, de-authentication Attacks)
Project
Badstore v1
Earn A Certificate
Why Join This Course?
Latest Technologies
Get Certified
Practical Demosntration
Project Based Learning
FAQs (Frequently Asked Questions)
Do I need Prior experience in programming?
Courses are designed from scratch by professionals. No prior knowledge is needed.
How is the course delivered?
The course is usually delivered through a combination of video lectures and projects.
What are the career prospects after completing the course?
Career opportunities for ethical hacking students include roles such as Ethical Hacker, Penetration Tester, and Security Analyst, where they assess and secure systems against cyber threats. With the increasing demand for cybersecurity expertise, professionals can find roles in diverse sectors, including technology, finance, healthcare, and government.
Use Coupon Code VITAL100 on checkout and get instant ₹100/- OFF on your next order!
Total Duration
Total Lessons
Course Validity
Level
Job Opportunities
Target Audience
- Security Analysts
- Compliance Officers
- Risk Managers
- Students and Graduates
- Business Continuity
- Planners
Follow Us On
Related Courses
Related products
-
Course
LinkedIn 360
₹800.00Original price was: ₹800.00.₹385.00Current price is: ₹385.00. Add to cart -
Course
SQL (Structured Query Language)
₹4,999.00Original price was: ₹4,999.00.₹599.00Current price is: ₹599.00. Add to cart -
Course
Front-End Development
₹4,999.00Original price was: ₹4,999.00.₹599.00Current price is: ₹599.00. Add to cart -
Course
UI / UX Designing
₹4,999.00Original price was: ₹4,999.00.₹599.00Current price is: ₹599.00. Add to cart